Other parts of this series:
They say insurance is a product that is sold not bought – and as a result, we often spend a lot of time focused on the buy-side: the risk landscape of potential customers, their coverage gaps, their servicing preferences… their apathy even. With cyber insurance though, buyers are strongly embracing the need for cover, recognising risk transfer as a key lever in the overall fight against cybercriminals.
But few businesses are actually buying cyber insurance right now. As cyber underwriters enter what we in our previous post termed a “hard market within a hard market”, the cost of protection is reaching unprecedented levels, making it unaffordable to all but the biggest players.
So, as the buy-side adopts an increasingly mature attitude, it’s the sell-side that remains unready, and we are yet to see a mass-market product that insurers can afford to write at the price point of most customers. Today’s post looks at some of the reasons for this disconnect between buyers and sellers, which goes back to the nature of cyber risks themselves: risks that share many, but by no means all, the characteristics of NatCat risks.
How smaller businesses woke up to their cybersecurity risk
Let’s start with the buy-side and how cyber insurance went from exotic beast to routine boardroom topic. After all, cyber policies are hardly new, having been in circulation in one form or another for around 20 years. So, why the recent entry into the mainstream?
What’s changed is that we’ve reached a tipping point in technology adoption. While large corporations have had major IT footprints for decades, this hasn’t always been true of small to medium-sized businesses (SMBs). Nowadays though, most enterprises are digital-first, all the way down to sole traders, and many have further embraced remote working and cloud computing. Cyber risk now affects everyone in every sector, and it affects them daily.
We can follow the expansion of the cyber conversation via some basic media analysis. The below graphic from Factiva – based on its archive of newspapers, newswires, industry publications, magazines and reports – charts the rise in unique articles referencing “cyber insurance”, from almost zero in 2012 to ~4,000/year in 2020. That figure is set to more than double in 2021. A similar trajectory can be traced for mentions of SMB cybersecurity.
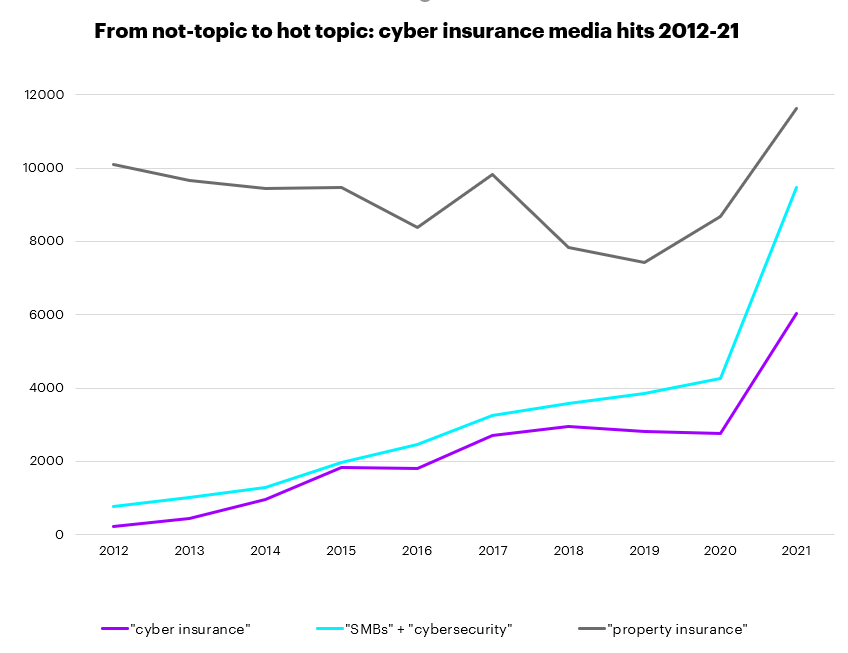
Source: Factiva (2021 figures represent a pro-rata adjustment of figures as of Sept. 2021)
The ever-loudening chatter around cybersecurity and cyber insurance has brought many new buyers to the table with risks in need of covering: from ransomware attacks and cyber-related business interruption to social engineering and data breaches.
With the buy-side dynamic plain to see, we now turn to the sell-side.
What we find here is really an ongoing struggle to provide affordable fit-for-purpose products. Or, in other words: insurers have not had as much success growing mass-market supply as they have growing mass-market demand.
These sell-side problems fall into two broad categories, part on the level of individual policies and risks, part on the portfolio level. Let’s look at both.

Cyber Insurance is now at an inflection point and poised for rapid growth. Discover more in our latest report Cyber Insurance: A profitable path to growth.
LEARN MORECleaning up bad cyber risks and bad cyber policies
The most apparent problem for insurers from all this incoming cyber demand is that many newly awoken firms, many of them SMBs, are fundamentally bad risks.
The reasons for this are simple. SMBs tend to operate less robust systems to begin with and have likely only made limited cybersecurity investments. Also, tech developments are increasing the attack surface for hackers, as more and more systems, devices and remote workers are added to company networks, something SMBs – with their lack of in-house legal, cyber and risk expertise, codified policies and staff training – are ill-equipped for.
These risk factors combine to raise the price floor for SMB cyber insurance, in much the same way as less-than-safe drivers, on average, get higher motor quotes. But help is at hand.
Just as drivers can see their risk – and therefore premiums – reduced via in-car safety features and telematics, much can be done at the front end to improve the cyber risk profile of small businesses.
This ranges from implementing basic cybersecurity hygiene, such as regular staff training and dual-factor authentication, to mandating specific cyber-defence software. By writing high-risk practices out of policies and incentivising good behaviour, insurers can engineer cyber risks down, reducing attritional losses and making small businesses more insurable. Lower base premiums should follow.
To firstly understand firms’ vulnerabilities – and secondly to plug them – insurers will need to tap the wider cybersecurity ecosystem extensively. This is already happening, with over 80% of sell-side players (including underwriters, brokers and agents) now using third-party technology vendors during cyber risk selection, especially for risk scanning, as per a recent survey by PartnerRe and Advisen.
How, primarily, do you use third-party vendors during cyber underwriting?

Cyber Insurance – The Market’s View; PartnerRe and Advisen, 2021
The ability to improve individual risks will certainly get better over time as insurers, brokers and cyber vendors gather more and more data. And standard cyber policies can be pruned to align with risk-management best practice as it emerges and evolves. However, for the cyber line to fully rise above its problems, changes are needed at the portfolio level too.
Unnatural catastrophes – why cyber remains a portfolio challenge
Cyber comes with the possibility of outsized losses at the portfolio level – due to the potential of major cyberattacks to affect many policyholders simultaneously. For this reason, cyber insurers need access to abundant capital, and it is little surprise that the line has relied heavily on reinsurance.
This isn’t a problem in itself, since capital has hardly been thin on the ground for commercial insurers in recent years. The problem for cyber reinsurers is really one not of capital volume but rather of capital efficiency. We see this if we compare cyber to other large-loss lines such as NatCat.
Reinsurers of natural catastrophes can write a lot of risk-off their capital pool because the chances of that pool being wiped out can be kept low through diversification. This is possible because natural catastrophes follow predictable annual and seasonal patterns, meaning you can create balanced portfolios. Large risk aggregations do occur, as different segments of your book take massive hits. But no aggregation is big enough to take down your whole book.
Or, in other words: it’s not Cat season everywhere at once.
But cyberspace knows no seasons. No matter how much you diversify your customer base – insuring clients in both hemispheres and across all continents – systemic risk remains substantial, with the potential to affect a critical mass of policyholders simultaneously. A hurricane in the Gulf of Mexico does not spread to other parts of the world like a virus. Ransomware attacks do. They are certainly catastrophic, but there’s nothing natural about them.
The net result is that reinsurers must hold a disproportionate amount of capital for the cyber risks they write – and higher rates are then required for the line to meet its cost of capital. Higher reinsurance rates translate into higher rates in the primary markets, meaning once again a higher price floor for cyber customers.
In practice, cyber risk – especially the threat of mega-aggregations – remains little understood. So, where capacity has been allocated, it has tended to be somewhat speculative in character, which explains why the market is dominated by a handful of major reinsurers.
This combination – a little reinsurance pool and a lot of speculation – exposes cyber insurance to severe corrections, since the whims of a single player, for example withdrawing from the line, can materially affect overall market capacity and, with it, the market rate. On top of already high prices, volatility will further hamper underwriters when it comes to building up a stable base of cyber customers – with all-around potential to stymie innovation in the line.
So, there we have it: the cyber sell-side problem. Prices are high for various reasons, some front-end, others back-end – and a variety of front-end and back-end solutions will be required to bring them down, something we explore in our next post.
Ultimately, experience in the market will reveal where risk-transfer solutions are most at home, as well as how to make them affordable. For this reason, insurers may be better served by an incremental approach to cyber risk – observing at a safe distance without getting swept away. In time, this “unnatural catastrophe” may not seem so unnatural after all. For more information, please download our newly released cyber insurance report. If you’d like to discuss any of the ideas in this series (or the report), don’t hesitate to get in touch.










